
 A Spotlight on the Security of Your MongoDB Database
A Spotlight on the Security of Your MongoDB DatabaseWhen Percona first published this blog in 2016, it was a refreshing comparison for important features of an enterprise-grade MongoDB deployment. But, comparing MongoDB Enterprise to Percona Server for MongoDB (PSMDB) has become such a common topic for discussion with Percona’s customers (and future customers) that the information from that original blog is now ingrained in my memory.
MongoDB and Percona have both come a long way since that blog was written. Several of the recommendations still hold true four years later, but some things have evolved on both sides. The purpose of this post is to expand upon and refresh the comparisons we made four years ago.
One thing that hasn’t changed is that security is still a top priority for all organizations in regard to their database environments. In the past year alone, there have been several high-profile data leaks due to misconfigured MongoDB databases.
It is important to note that these highly publicized leaks are often due to configuration issues, or unsupported, out-of-date, software. If you are using up-to-date, well-maintained, properly implemented deployments of MongoDB, there is no great reason to fear.
In this post I will explain the security options that exist in open source MongoDB software. These options allow you to deploy a secure, enterprise-grade, MongoDB deployment without worrying about license fees. This is important because it allows organizations the flexibility to deploy consistent models across their entire infrastructure. Too often we see customers running different versions of software in dev/test/qa due to license restrictions. With open source software, this is not a concern.
One thing that has changed since the original blog was written is the growth explosion of the Database as a Service (DBaaS) sector of database management. DBaaS is a more specific form of Platform as a Service (PaaS).
MongoDB, Inc. has gone all-in on the DBaaS space. This aligns well with its continued mission to empower developers by overcoming the database management burden.
In 2016, MongoDB Atlas went GA as MongoDB’s DBaaS offering. In 2017, MongoDB went public on the Nasdaq. In 2018, MongoDB acquired a competitor in the space – MLab. The most significant recent change has been its switch to a new license, SSPL. This directly impacts companies offering “as a service” solutions of MongoDB.
According to MongoDB’s CEO, MongoDB’s long-term strategy involves Enterprise-licensed software subscriptions, of which DBaaS components will be heavily integrated.
So, if vendor lock-in and utilizing truly open source technology are a priority for your company, what are your options? This is an area where I will expand on Percona’s original security-centric blog post, and explain the options and paths that exist for users who do not want to double-down on MongoDB’s enterprise-licensed toolkit.
There are many aspects that are important to running an Enterprise-grade version of MongoDB are:
In this blog we are looking specifically at Security. For a database this means:
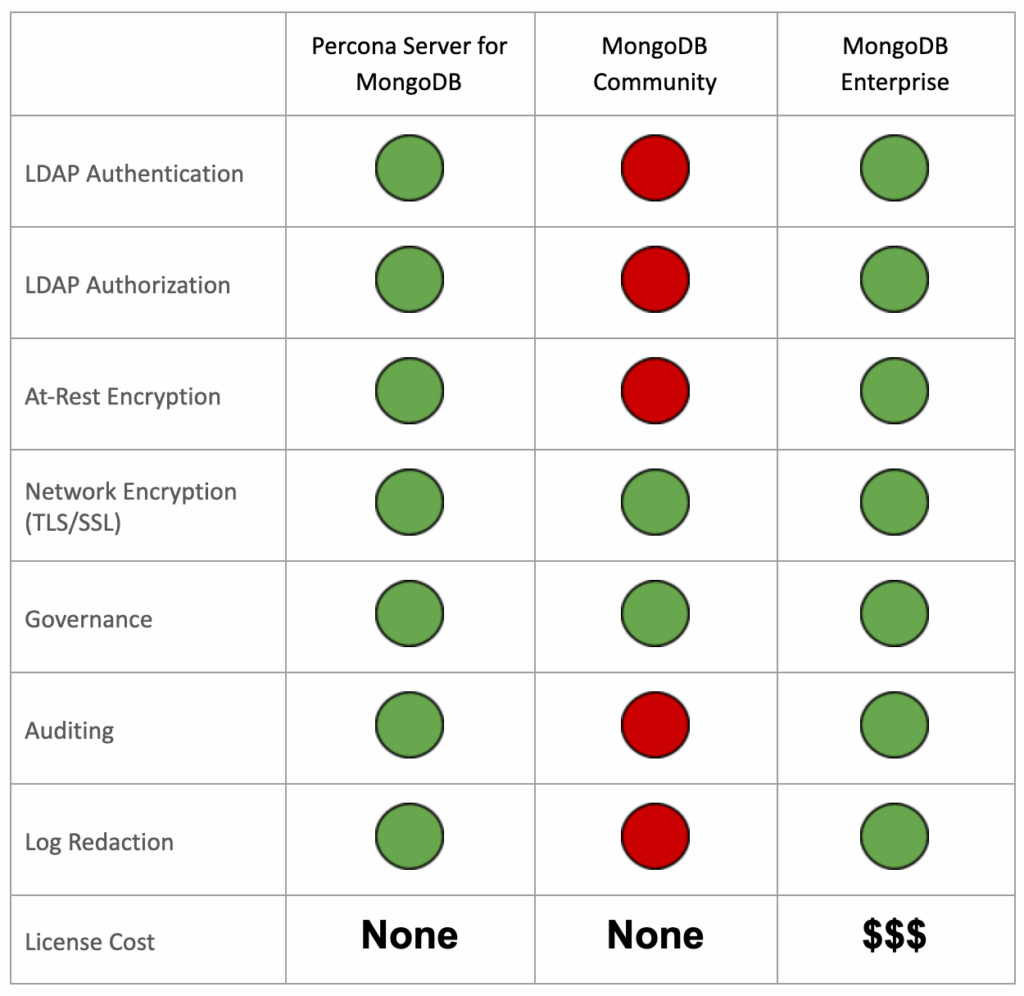
MongoDB has built-in users. It misses things, however, like password complexity, age-based rotation, centralization, and identification of user roles versus service functions. This has been submitted as a feature request but is backlogged, with no planned fix version.
These user authentication controls are essential to passing PCI. PCI requires that people don’t use old or easy-to-break passwords and that user access is revoked when there is a change in status (such as someone leaving a department or the company). The reason that this logic has not been added at the database level is that, for the most part, another answer exists that integrates easily with MongoDB. LDAP is an open-source project of its own. Many connectors allow the use of Windows Active Directory (AD) systems to talk with LDAP.
The community version of MongoDB does not have this functionality:
A final note about authentication is Kerberos authentication. Percona Server for MongoDB and MongoDB Enterprise both have implemented this feature. It is available in PSMDB 4.2.6 or higher.
Role-based Authorization is core to MongoDB Community, MongoDB Enterprise, and Percona Server for MongoDB. In every release since Mongo 2.6, you can use built-in roles, or even craft your own down to what actions someone might be able to do – only exposing exactly what you want users to be able to do. This is a core MongoDB feature that is everywhere, and in every build, regardless of vendor.
MongoDB Enterprise and Percona Server for MongoDB have integrated LDAP authorization into their database solutions. This feature maps LDAP group distinguished names to MongoDB group roles and allows for easy role configuration among groups of users. This is available in versions 4.2.5 or higher for PSMDB.
Encryption at the database layer has become increasingly popular and is mandatory at large organizations due to recent data compromises and breaches. Although most high-profile breaches are a result of improperly implemented, or extremely out-of-date, deployments, additional security measures like encryption at-rest and in-flight are always preferred. Encryption is often a requirement for databases operating under PCI or HIPAA standards.
The first aspect of encryption is in-flight or over-the-wire encryption. This ensures that network traffic is only readable by the intended client. Luckily, this is another core feature of the MongoDB code and is present in every build, regardless of vendor. Percona recommends standardizing on OpenSSL as it is likely to have compatibility across open source databases, and open source operating system platforms.
The second aspect of encryption is at-rest encryption. This ensures that once stored, data can only be read by the intended client. This option is available for the WiredTiger storage engine. MongoDB’s implementation requires a MongoDB Enterprise License. Luckily, Percona has you covered with an open source implementation of WiredTiger encryption in Percona Server for MongoDB. Percona’s implementation has Hashicorp Vault integration for key management, and also encrypts rollback files, which could contain sensitive data.
MongoDB’s concept of Schema Validation ensures that standards for storing data are defined and rigidly enforced if necessary. All versions of MongoDB have methods for enforcing format standards for data stored in the database. DBAs can check for field names based on certain criteria based on regex strings to search for SSN or CC numbers. MongoDB’s native JSON language allows for easy scripting of customized options, regardless of MongoDB version, as this is a core part of the MongoDB database. By enforcing rigid schemas, organizations can ensure that developers do not insert sensitive data into documents that do not belong.
The concept of auditing user activity is not foreign to anyone responsible for security. It is a critical aspect of compliance for all organizations. This is another area where Percona can offer an open source alternative to MongoDB’s Enterprise license. On the MongoDB side, this is an Enterprise-only feature that requires a license. On the Percona side, this is included as part of Percona Server for MongoDB. They are very similar in functionality and allow users to filter output to particular users, databases, collections, or sources. This allows granularity into what is audited and allows the review logs in the event of a security incident.
Another important MongoDB security consideration is log redaction. Often, it is necessary to remove messages from a log event before logging. This will prevent the logs from containing potentially sensitive information like PII to the diagnostic log. Metadata such as error or operation codes, line numbers, and source file names remain visible in the logs.
This is an Enterprise-only feature on the MongoDB, Inc. side, Percona Server for MongoDB offers Log Redaction functionality in its open source version. It is important to note that while this feature increases security, it can make troubleshooting more difficult.
The purpose of this blog was to inform those interested in MongoDB of the alternative options available and provide information to enable them to select the most appropriate MongoDB database software for their business.
Security is an important reason why many companies opt for the Enterprise version of MongoDB. However, Percona Server for MongoDB can offer all of this functionality with a non-licensed model. This means no more worrying about purchasing licenses for production, dev, test, qa, sandbox, etc. You can ensure consistent deployment across all environments by utilizing non-licensed, open source software, all while ensuring that the security standards required by your organization are being met.
The chart below summarizes what we’ve covered:
As well as our free open source MongoDB software, Percona Server for MongoDB, and Percona Backup for MongoDB, we recently launched Percona Distribution for MongoDB.
Percona Distribution for MongoDB is an open source enterprise MongoDB solution. It helps you ensure data availability for your applications while improving security and simplifying the development of new applications in the most demanding public, private, and hybrid cloud environments.
We also offer specialized support, consulting, and managed services for MongoDB databases:
For more information, download our free white paper to learn why more and more enterprise companies are leaning in when it comes to adopting open source software (OSS). It examines the benefits of adopting open source into your database infrastructure, and how your business can benefit from having an open source product as part of your enterprise solutions.
Resources
RELATED POSTS
Why does this article conflict with
https://www.percona.com/software/mongodb/feature-comparison
Hi Laurence,
I am happy to address any discrepancies. Can you be more specific about where you are seeing conflicting information? Thanks!