
It’s easy to enable Amazon RDS remote access when launching an Amazon RDS instance, but there can be many issues. I created this blog as a guide describing the various issues/configurations we might encounter.
As the first step, we need to select a VPC where we will launch our Amazon RDS instance. The default VPC has all the required settings to make the instance remotely available; we just have to enable it by selecting “Yes” at Public accessibility.
For this example, we used the Default VPC and asked AWS to create a new security group.
Once the instance is created, we can connect to the “Endpoint” address:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 |
[root@server1 ~]# mysql -h publicdb.cbnuzwwzlcf1.eu-west-3.rds.amazonaws.com -u dbuser -p Enter password: XXXXXX mysql> s -------------- mysql Ver 14.14 Distrib 5.7.19-17, for Linux (x86_64) using 6.2 Connection id: 14 Current database: Current user: dbuser@server1.hostname.com SSL: Cipher in use is AES256-SHA Current pager: stdout Using outfile: '' Using delimiter: ; Server version: 5.6.37 MySQL Community Server (GPL) Protocol version: 10 Connection: publicdb.cbnuzwwzlcf1.eu-west-3.rds.amazonaws.com via TCP/IP Server characterset: latin1 Db characterset: latin1 Client characterset: utf8 Conn. characterset: utf8 TCP port: 3306 Uptime: 1 min 56 sec Threads: 2 Questions: 9986 Slow queries: 0 Opens: 319 Flush tables: 1 Open tables: 80 Queries per second avg: 86.086 -------------- mysql> |
When AWS creates the security group after we select the option to make it publicly accessible, it appears that AWS takes care of everything. But what if we check the created security groups?
It created a rule to enable incoming traffic, as security group works as a whitelist (it denies everything except the matching rules).
As we can see here, AWS only created the inbound rule for my current IP address, which means once we change IPs or try to connect from another server, it will fail. To get around that, we need to add another rule:
Adding the 0.0.0.0/0 rule opens the port for the world. This is dangerous! Since anyone can try connecting, it’s much better if we can supply a list of IPs or ranges we want to be enabled for remote access, even from outside of AWS.
To run RDS in a new VPC or in an existing VPC, we need to ensure a couple of things.
The VPC needs to have at least two subnets. We believe this is something Amazon asks so that the VPC is ready if you choose to move to a Multi-AZ master, or to simply spread the read-only instances across multiple AZ for higher availability.
If you want to make the RDS cluster remotely available, we need to attach an IGW (Internet Gateway) to the VPC. If you don’t, it isn’t able to communicate with the outside world. To do that, go to VPC -> Internet gateways and hit “Create Internet Gateway”:
Once it’s created, select “Attach to VPC” and select your VPC.
Still, you won’t be able to reach the internet as we need to add route towards the newly attached internet gateway.
To do that, go to “Route Tables” and select our VPC, and add the following route (0.0.0.0/0 means it’s going to be the default gateway, and all non-internal traffic needs to be routed towards it):
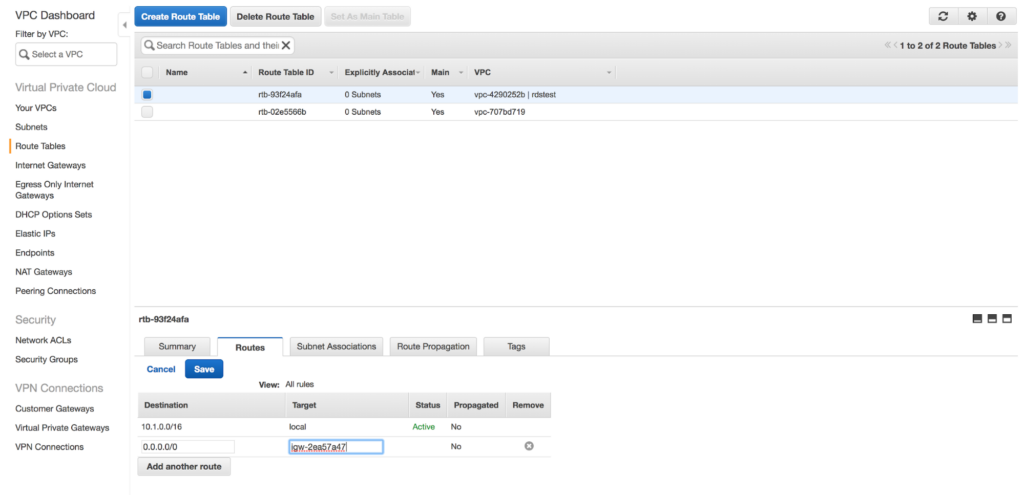
Hit Save. Now the VPC has Internet access, just like AWS’s Default VPC.
Need help with your cloud migration? Contact us today.
Resources
RELATED POSTS
Thank you for sharing!
Thank you Janos,
Have you done something similar for RDS Aurora/MySQL Serverless? It don’t seem to be publicly available from what I am seeing.
am i right that amazon rds has not the same functionality like google cloud sql with its proxy file?
I’m just going to post it here for someone who would get in the same situation as me.
I wasn’t being able to connect to my RDS database. I’ve manually reviewed any detail and everything was alright. There were no indications of any issues whatsoever and I couldn’t find any suitable information in the documentation. My VPC was configured with narrow CIDR: 10.0.0.0/22 and each subnet had a 255 addresses. After I’ve changed CIDR to 10.0.0.0/16 and split it totally between two subnets my RDS connection started to working. It was a pure luck that I’ve managed to find a source of the problem, because it doesn’t make any sense.